OSINT Sources – Using Geolocation for OSINT Investigations
Geolocation OSINT
Geolocation OSINT, or Open Source Intelligence, represents a pivotal facet of modern investigative methodologies, focusing on extracting actionable insights from publicly available data to ascertain the geographical location of individuals, entities, or events. In essence, it harnesses the vast troves of information scattered across the digital landscape, ranging from social media platforms to satellite imagery repositories, to unravel the spatial dimensions of a subject under scrutiny.
Geolocation OSINT stands as a cornerstone technique, enabling analysts to transcend traditional boundaries and paint a comprehensive picture of the subject’s movements, affiliations, and activities. By amalgamating geospatial data with open-source intelligence, investigators can unveil hidden connections, anticipate potential threats, and formulate informed decisions.
Importance of Geolocation in OSINT Investigations
The significance of geolocation within OSINT investigations cannot be overstated, as it serves as the linchpin for contextualising disparate data points and transforming raw information into actionable intelligence. By pinpointing the geographic coordinates associated with a target, analysts can narrow their focus, delving deeper into the socio-political, economic, or security implications of their findings.
In an era defined by the ubiquity of digital footprints, geolocation data provides a veritable goldmine of insights, offering a window into the spatial dynamics of human behaviour and interaction. Whether tracking the movements of adversarial actors, monitoring the spread of disinformation campaigns, or conducting geospatial risk assessments, the ability to harness geolocation within OSINT investigations empowers stakeholders across diverse sectors to make informed decisions and mitigate potential risks.
Key Elements of Geolocation OSINT
- Metadata Extraction: At the core of geolocation OSINT lies the extraction and analysis of metadata embedded within digital files, such as photos, videos, or documents. These metadata payloads often harbour invaluable nuggets of geospatial information, including GPS coordinates, timestamps, and device identifiers, which can be leveraged to ascertain the origins and whereabouts of the content.
- Social Media Analysis: Social media platforms serve as fertile grounds for geolocation OSINT, with users routinely sharing location-tagged posts, check-ins, and photographs. By scrutinising these digital breadcrumbs, analysts can map out the spatial footprint of individuals or events, shedding light on their movements, affiliations, and interests.
- Mapping Tools: Geolocation OSINT practitioners rely on an array of mapping tools and geographic information systems (GIS) to visualise and analyse spatial data. Platforms such as Google Maps, Bing Maps, and Esri ArcGIS empower analysts to overlay geospatial layers, perform spatial queries, and conduct proximity analyses, facilitating the interpretation of location-based intelligence.
- IP Geolocation: Every device connected to the internet is assigned a unique IP address, which can be geolocated to determine its physical location. IP geolocation techniques enable analysts to trace the origins of digital communications, identify potential threat actors, and uncover network infrastructures associated with malicious activities.
- Satellite Imagery: Satellite imagery platforms, including Google Earth and DigitalGlobe, offer high-resolution snapshots of the Earth’s surface, enabling analysts to conduct remote reconnaissance and monitor changes in the environment. By juxtaposing satellite imagery with geospatial data layers, investigators can identify landmarks, infrastructure assets, and anomalous patterns indicative of illicit activities.
- Crowdsourcing and Collaboration: Geolocation OSINT thrives on collaboration and collective intelligence, with online communities and forums serving as hubs for sharing insights, techniques, and tools. Through collaborative efforts, analysts can pool their expertise, verify findings, and tackle complex geolocation challenges with greater efficiency and accuracy.
The fusion of geolocation techniques with open-source intelligence heralds a new era of investigative prowess, wherein the spatial dimensions of information serve as a compass guiding stakeholders towards deeper insights and informed decision-making. By mastering the key elements of geolocation OSINT, analysts can navigate the digital terrain with confidence, unraveling the mysteries concealed within the vast expanse of open-source data.
Methods of Geolocation OSINT
Geolocation OSINT, or Open Source Intelligence, employs various methods to gather and analyse location-based information from publicly available sources. From metadata analysis in digital files to social media monitoring and satellite imagery examination, these methods offer insights crucial for tracking individuals, events, or objects across geographical locations. Geolocation OSINT techniques provide valuable intelligence for law enforcement, cybersecurity, disaster response, and investigative purposes.
Metadata Extraction
A. Explanation of Metadata
Metadata refers to the descriptive information embedded within digital files, providing insights into various aspects of the file’s creation, modification, and content. In the context of geolocation OSINT, metadata often includes details such as GPS coordinates, date and time stamps, camera settings, and device information. This hidden layer of data can be invaluable for geolocating individuals, events, or objects captured in digital media.
B. Types of Metadata
- EXIF Data: Exchangeable Image File Format (EXIF) is a standard for storing metadata in image files. It typically includes details such as camera make and model, aperture, shutter speed, ISO settings, and GPS coordinates if available.
- IPTC Data: The International Press Telecommunications Council (IPTC) standardises metadata for news and media content. IPTC data may include information about the photographer, copyright, location, and caption.
- XMP Data: Extensible Metadata Platform (XMP) is an Adobe standard used for embedding metadata in various file formats, including images, videos, and PDFs. XMP data can include geospatial information, copyright details, and workflow-related metadata.
C. How to Extract Metadata from Digital Files
Extracting metadata from digital files can be accomplished using a variety of tools and techniques:
- Metadata viewers and editors: Software tools like ExifTool, Metadata++ (for Windows), or Preview (for Mac) allow users to view and edit metadata directly.
- Online metadata extraction tools: Websites such as Jeffrey’s Image Metadata Viewer or ExifData.com enable users to upload files and extract metadata online.
- Command-line utilities: For advanced users, command-line tools like ExifTool or Exiv2 provide powerful options for extracting metadata in batch operations.
D. Case Studies Demonstrating Metadata Analysis
- Geolocating Criminal Suspects: Law enforcement agencies have successfully used metadata from photos shared on social media to pinpoint the locations of criminal suspects. By analysing EXIF data, investigators can determine where and when a photo was taken, aiding in suspect identification and apprehension.
- Verifying Authenticity of Images: Journalists and fact-checkers utilise metadata analysis to verify the authenticity of images circulating online. By examining metadata for inconsistencies or anomalies, they can assess the credibility of visual content and detect potential manipulation or misinformation campaigns.
- Tracking Wildlife Movements: Conservationists and researchers employ metadata from wildlife photos to track animal movements and behaviours. By analysing GPS coordinates embedded in photos, scientists can monitor migration patterns, habitat usage, and population dynamics, aiding in wildlife conservation efforts.
Social Media Analysis
A. Importance of Social Media in Geolocation OSINT
Social media platforms serve as rich sources of geolocation data, with users often sharing their whereabouts through posts, check-ins, and tagged locations. Geolocation OSINT analysts leverage social media to gather real-time intelligence, track events, and locate individuals of interest.
B. Types of Geolocation Data Found on Social Media
- Check-ins and Location Tags: Users voluntarily share their current or past locations by checking in at restaurants, landmarks, or events. Location tags in posts and photos provide additional geospatial context.
- Geotagged Posts and Photos: Many social media platforms allow users to attach GPS coordinates to their posts and photos, enabling precise geolocation of content.
- Metadata from Shared Media: Photos and videos shared on social media often contain embedded metadata such as GPS coordinates, timestamps, and device information, offering valuable clues about the location and context of the content.
C. Tools and Techniques for Extracting Geolocation Data from Social Media
Extracting geolocation data from social media involves a combination of manual examination and automated tools:
- Manual Review: Analysts manually review posts, photos, and profiles to identify geolocation cues such as text descriptions, hashtags, and location tags.
- Geolocation APIs: Social media APIs such as the Twitter API or Instagram Graph API provide access to geolocation data associated with user posts and media.
- Social Media Monitoring Tools: Commercial OSINT tools like Echosec, Geofeedia, or Hootsuite Insights offer geospatial capabilities for monitoring social media activity in specific locations or regions.
D. Case Studies of Successful Social Media Geolocation Investigations
- Disaster Response and Crisis Management: Emergency responders utilise social media geolocation data to assess the impact of natural disasters and coordinate rescue efforts. By monitoring posts and tweets from affected areas, responders can identify critical needs and allocate resources effectively.
- Investigating Protest Movements: Law enforcement agencies and intelligence analysts track protest movements and civil unrest by analysing social media activity. Geolocating protest-related posts and videos helps authorities anticipate crowd movements, identify key organisers, and mitigate potential conflicts.
- Locating Missing Persons: Family members and law enforcement agencies leverage social media platforms to seek assistance in locating missing persons. By sharing photos, descriptions, and last-known locations, social media users can aid in the search efforts and reunite missing individuals with their loved ones.
Mapping Tools
A. Overview of Mapping Tools
Mapping tools provide interactive interfaces for visualising geographical data and conducting spatial analysis. These tools range from consumer-oriented platforms like Google Maps to specialised Geographic Information Systems (GIS) software used in professional settings.
B. Commonly Used Mapping Platforms (Google Maps, Bing Maps, etc.)
- Google Maps: Google Maps is a widely used mapping service offering satellite imagery, street-level views, and route planning features. It provides APIs for embedding maps into websites and mobile applications.
- Bing Maps: Bing Maps, developed by Microsoft, offers similar functionality to Google Maps, including satellite imagery, street maps, and geocoding services.
- OpenStreetMap: OpenStreetMap is a collaborative mapping project where users contribute and edit map data. It provides free access to geographic data and is widely used for custom mapping applications.
C. How Mapping Tools Aid in Geolocation Investigations
Mapping tools facilitate geolocation investigations by visualising geospatial data and enabling spatial analysis:
- Geotagging Analysis: Analysts overlay geotagged media and social media posts onto maps to identify spatial patterns and hotspots of activity.
- Route Planning: Investigators use mapping tools to reconstruct and analyse the movement paths of individuals or vehicles captured in geolocated data.
- Geofencing: Law enforcement agencies employ geofencing techniques to define virtual boundaries and monitor activity within specific geographic areas, such as crime scenes or restricted zones.
D. Advanced Techniques for Mapping and Visualisation
Advanced mapping techniques enhance the capabilities of geolocation investigations:
- 3D Mapping: Three-dimensional mapping tools like Google Earth Pro enable users to visualise terrain features, buildings, and landscapes in realistic 3D models.
- Heatmaps: Heatmap visualisations highlight areas of high density or intensity based on geospatial data, providing insights into spatial trends and distributions.
- Spatial Analysis: GIS software offers advanced spatial analysis tools for measuring distances, calculating spatial relationships, and conducting geostatistical analysis.
IP Geolocation
A. Explanation of IP Geolocation
IP geolocation is the process of determining the geographical location of an IP address based on various data points associated with the IP address, such as its numerical address, network, and registration information. This technique allows OSINT investigators to approximate the physical location of internet-connected devices, including computers, smartphones, and IoT devices.
B. How IP Geolocation Works
IP geolocation works by correlating IP address data with geographic information stored in databases maintained by internet service providers (ISPs), geolocation companies, and regional internet registries (RIRs). These databases contain records mapping IP addresses to specific locations, such as cities, regions, or countries. When a user accesses the internet, their IP address is logged by web servers and can be cross-referenced with these databases to determine their approximate geographical location.
C. IP Geolocation Databases and Tools
Several commercial and free IP geolocation databases and tools are available to OSINT investigators:
- MaxMind GeoIP: MaxMind offers a popular IP geolocation database and API used by businesses, security professionals, and researchers for locating IP addresses worldwide.
- IP2Location: IP2Location provides IP geolocation data services, including databases, APIs, and web-based tools for identifying the geographic location of IP addresses.
- Whois Lookup: WHOIS databases maintained by domain registrars and RIRs contain registration information for IP addresses, domain names, and autonomous system numbers (ASNs), which can be useful for geolocating IP addresses.
D. Real-world Applications of IP Geolocation in OSINT Investigations
IP geolocation is utilised in a variety of OSINT investigations across different domains:
- Cybersecurity: Security analysts leverage IP geolocation to trace the origins of cyber attacks, identify malicious actors, and block traffic from suspicious IP addresses.
- Digital Forensics: Forensic examiners use IP geolocation to trace the online activities of suspects, track the dissemination of digital evidence, and reconstruct digital footprints in criminal investigations.
- Geopolitical Analysis: Researchers and analysts study IP geolocation data to monitor internet censorship, geopolitical events, and regional connectivity trends, providing insights into global internet infrastructure and digital sovereignty issues.
Satellite Imagery
A. Importance of Satellite Imagery in Geolocation
OSINT Satellite imagery plays a crucial role in geolocation OSINT by providing high-resolution visual data of locations worldwide. Analysts leverage satellite imagery for reconnaissance, surveillance, and monitoring applications across various sectors, including defence, environmental monitoring, and urban planning.
B. Overview of Satellite Imagery Platforms (Google Earth, DigitalGlobe, etc.)
- Google Earth: Google Earth is a widely used virtual globe and mapping software that provides access to high-resolution satellite imagery, aerial photography, and 3D terrain models. It offers both desktop and web-based versions, as well as APIs for developers.
- DigitalGlobe: DigitalGlobe, now part of Maxar Technologies, is a leading provider of commercial satellite imagery and geospatial solutions. Its constellation of high-resolution satellites captures imagery of Earth’s surface for a variety of applications, including mapping, disaster response, and urban planning.
- Sentinel Hub: Sentinel Hub is a cloud-based platform offering access to satellite imagery from the European Space Agency’s Sentinel satellites. It provides multispectral data, time-lapse imagery, and customisable processing workflows for geospatial analysis.
C. How to Use Satellite Imagery for Geolocation Investigations
Analysts use satellite imagery for various geolocation tasks, including:
- Identifying Features: Analysts identify landmarks, infrastructure, and terrain features visible in satellite imagery to provide context for geolocated events or objects.
- Verifying Locations: Satellite imagery is used to verify the accuracy of geolocation data obtained from other sources, such as social media posts or GPS coordinates embedded in digital media.
- Monitoring Changes: Analysts monitor changes in the environment, such as deforestation, urban expansion, or natural disasters, by comparing satellite imagery over time and detecting spatial and temporal trends.
D. Case Studies Illustrating Satellite Imagery Analysis
- Disaster Response: Humanitarian organisations use satellite imagery to assess the extent of damage caused by natural disasters, such as hurricanes, earthquakes, or wildfires, and coordinate emergency response efforts.
- Environmental Monitoring: Researchers track environmental changes, such as glacier retreat, sea level rise, or deforestation, using satellite imagery to study the impacts of climate change and human activities on Earth’s ecosystems.
- Military Intelligence: Defence and intelligence agencies utilise satellite imagery for reconnaissance, surveillance, and monitoring of strategic locations, military installations, and potential threats to national security.
Crowdsourcing and Collaboration
A. The Power of Crowdsourcing in OSINT
Crowdsourcing harnesses the collective intelligence and expertise of a diverse group of individuals to gather, analyse, and verify information from open sources. In geolocation OSINT, crowdsourcing enables distributed collaboration and resource-sharing among analysts, researchers, and volunteers worldwide.
B. Online Communities and Forums Dedicated to OSINT
- Reddit: Subreddits such as r/OSINT and r/Intelligence serve as online communities where OSINT practitioners share insights, discuss tools and techniques, and collaborate on geolocation investigations.
- Twitter: OSINT professionals and researchers use Twitter to exchange information, share discoveries, and engage in discussions on topics related to geolocation, cybersecurity, and open-source intelligence.
- Discord: Discord servers dedicated to OSINT, cybersecurity, and digital forensics provide platforms for real-time communication, knowledge-sharing, and collaboration among members of the OSINT community.
C. Collaborative Tools and Platforms for OSINT Investigations
- IntelTechniques: IntelTechniques offers a range of OSINT tools and resources, including online courses, e-books, and forums, to support investigators in conducting geolocation OSINT investigations.
- Bellingcat: Bellingcat is an investigative journalism platform that utilises open-source information and geolocation techniques to investigate and verify news stories, human rights abuses, and conflict zones.
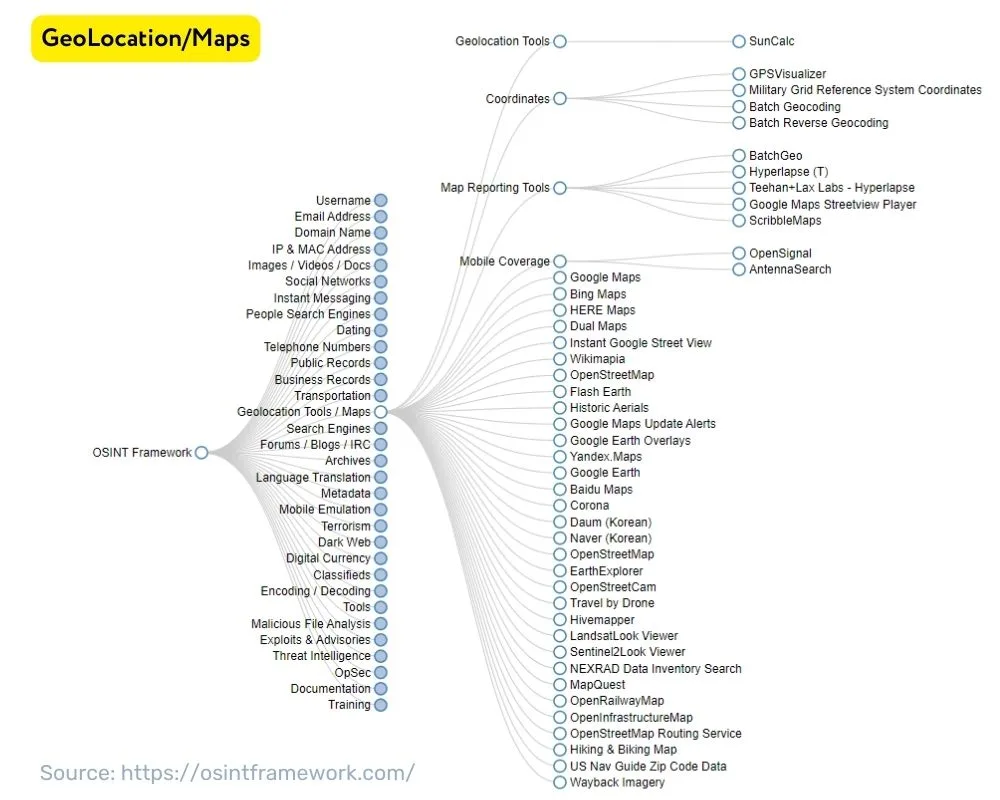
- OSINT Framework: OSINT Framework is a curated collection of OSINT tools, resources, and techniques categorised by different investigation phases, such as reconnaissance, analysis, and reporting.
D. Benefits and Challenges of Crowdsourced Geolocation Intelligence
Benefits:
-
- Diverse Perspectives: Crowdsourcing brings together individuals with diverse backgrounds and expertise, enriching geolocation investigations with multiple perspectives and insights.
- Rapid Response: Crowdsourcing enables real-time collaboration and information-sharing, allowing investigators to respond quickly to emerging events and situations.
- Scalability: Crowdsourcing scales the capacity and resources available for geolocation OSINT investigations, empowering larger communities to tackle complex challenges collaboratively.
Challenges:
-
- Information Quality: Crowdsourced data may vary in quality and reliability, requiring careful verification and validation to ensure accuracy and trustworthiness.
- Security Concerns: Crowdsourcing sensitive information or conducting investigations in high-risk environments may expose participants to security risks, necessitating privacy protection measures and secure communication channels.
- Coordination and Management: Coordinating and managing large crowdsourced projects can be challenging, requiring effective leadership, communication, and task allocation to ensure productive collaboration and meaningful contributions.
How OSINT Tools Enhance Geolocation Investigations
OSINT tools streamline and automate various aspects of geolocation investigations, including data collection, analysis, and visualisation:
- Data Aggregation: OSINT tools aggregate data from multiple sources, enabling investigators to gather geolocation data from diverse platforms and formats.
- Link Analysis: Tools like Maltego facilitate link analysis and visualisation, helping investigators identify relationships and connections between geolocated entities, such as individuals, locations, and events.
- Automation: OSINT tools automate repetitive tasks and workflows, saving time and effort in geolocation investigations and enabling analysts to focus on higher-level analysis and interpretation.
Ethical Considerations
A. Importance of Ethics in Geolocation
OSINT Ethical considerations are paramount in geolocation OSINT to ensure that investigations are conducted responsibly, respectfully, and lawfully. Ethical conduct fosters trust, integrity, and credibility in OSINT practice and upholds the rights and privacy of individuals and communities.
B. Ethical Guidelines for Conducting Geolocation Investigations
OSINT practitioners should adhere to ethical guidelines and principles when conducting geolocation investigations:
- Respect Privacy: Obtain information from publicly available sources and refrain from intruding into private or restricted areas without proper authorisation or consent.
- Maintain Integrity: Conduct investigations with honesty, objectivity, and transparency, disclosing any conflicts of interest or biases that may influence the findings or conclusions.
- Legal Compliance: Comply with relevant laws, regulations, and ethical standards governing OSINT practice, including data protection laws, intellectual property rights, and jurisdictional considerations.
C. Legal Considerations and Privacy Laws
Geolocation OSINT investigations may be subject to legal and regulatory requirements concerning privacy, data protection, and surveillance:
- Data Protection Regulations: Ensure compliance with data protection regulations, such as the General Data Protection Regulation (GDPR) in the European Union, when collecting and processing personal data for geolocation investigations.
- Surveillance Laws: Be aware of laws governing surveillance, interception, and monitoring activities in different jurisdictions, as geolocation OSINT investigations may implicate privacy rights and civil liberties.
- Jurisdictional Issues: Consider the legal jurisdiction of the entities involved in geolocation investigations, including individuals, organisations, and data sources, to determine the applicable laws and regulatory requirements.
D. Best Practices for Ethical Geolocation OSINT
Adopt best practices to promote ethical conduct and integrity in geolocation OSINT:
- Informed Consent: Obtain informed consent from individuals whose data may be collected or analysed in geolocation investigations, especially in cases involving sensitive or personally identifiable information.
- Data Minimisation: Minimise the collection and retention of unnecessary data in geolocation investigations to reduce the risk of privacy violations and data misuse.
- Transparency and Accountability: Maintain transparency and accountability throughout the geolocation OSINT process, documenting methodologies, sources, and findings to facilitate auditability and reproducibility.
Examples of Successful Geolocation OSINT Investigations
- Law Enforcement: Investigating criminal activities, locating fugitives, and gathering evidence using geolocation data from digital media and online sources.
- Humanitarian Aid: Supporting disaster response efforts, identifying vulnerable populations, and coordinating relief operations with geospatial intelligence and crowdsourced data.
- Environmental Conservation: Monitoring wildlife habitats, tracking illegal logging or poaching activities, and enforcing environmental regulations using satellite imagery and geospatial analysis.
- Geopolitical Conflicts: Mapping territorial disputes, monitoring military movements, and assessing geopolitical risks using satellite imagery and geospatial analysis.
- Cybersecurity Threats: Tracing the origins of cyber attacks, identifying threat actors, and mitigating security breaches using IP geolocation and network forensics.
- Disinformation Campaigns: Detecting and debunking misinformation, tracking the spread of fake news, and uncovering disinformation networks through social media analysis and metadata forensics.
Manage Business Risk with OSINT.
Neotas is an Enhanced Due Diligence Platform that leverages AI to join the dots between Corporate Records, Adverse Media and Open Source Intelligence (OSINT).
Extract, analyse, and visualise data from Geolocation. Speed up your investigations with Geolocation intelligence data.
Schedule a Call or Book a Demo of Neotas Enhanced Due Diligence Platform.
Read More about Open Source Intelligence:
- OSINT Framework, OSINT Tools, OSINT Techniques, and how to use OSINT framework.
- What is the OSINT Framework and how to use it?
- Open Source Intelligence (OSINT) in the Fight Against Financial Crime
- Reduce & Manage Business Risk with Neotas Open Source Intelligence (OSINT) Solutions
- Open Source Intelligence (OSINT) based AML Solution sees beneath the surface
- Enhancing ESG Risk Management Framework with Neotas’ OSINT Integration
- How Open Source Intelligence (OSINT) is transforming enhanced due diligence and investigations in AML compliance
- Detecting Modern Slavery In Your Supply Chain using Open-source Intelligence
- Creating an effective framework for managing risk with suppliers and third parties using open-source intelligence (OSINT)
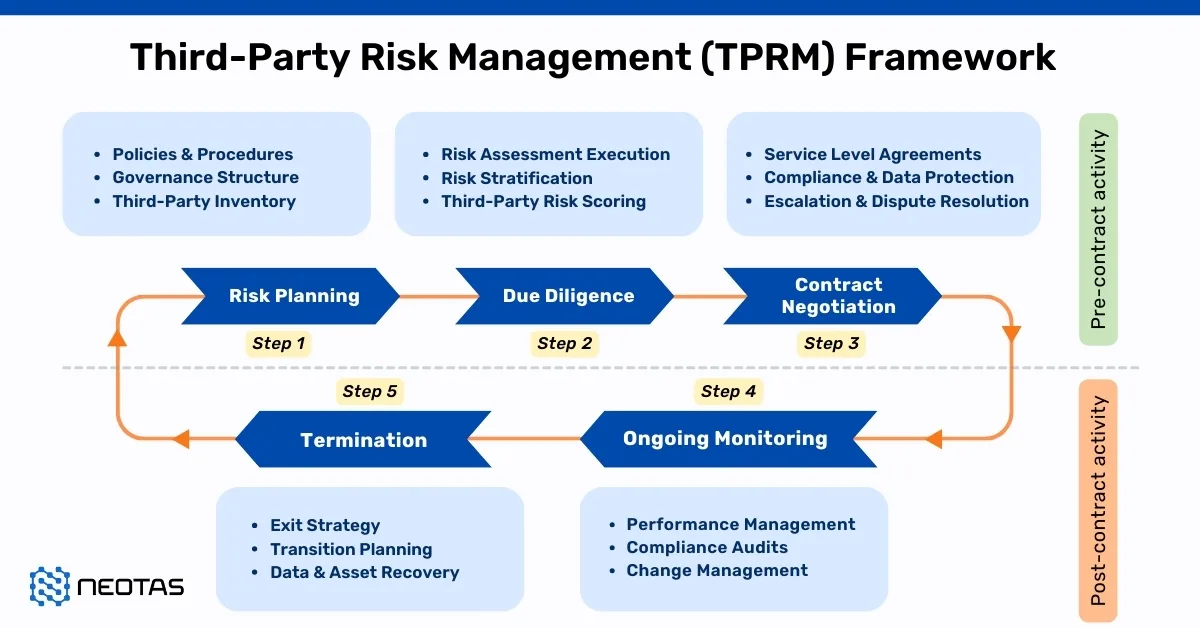
- Third Party Risk Management (TPRM) Using OSINT
- Open-source Intelligence For Supply Chain – OSINT
- ESG Risk Management Framework with Neotas’ OSINT Integration
- Open Source Intelligence In AML Compliance | Case Study
- Identifying Difficult And Dangerous Senior Managers
- ESG Risk Investigation Uncovers Supply Chain Risks
- Financial Crime Compliance & Risk Management Trends
- Network Analysis Reveals International Links In Credit Risk Case
- Network Analysis and Due Diligence – Terrorist Financing
- Using OSINT For Sources Of Wealth Checks
- ESG Risks Uncovered In Investigation For Global Private …
- PEP Screening: Undisclosed Political Links Uncovered For European Organisation
- Risk-Based Approach (RBA) to AML & KYC risk management
- Anti-Money Laundering (AML)
- Supply Chain Risk Management
- Using Open Source Intelligence For Enhanced Due Diligence